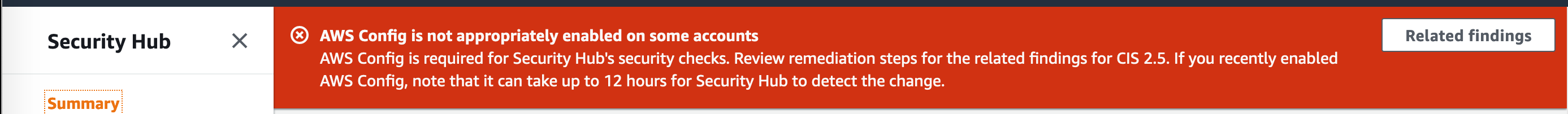
Have you deployed Control Tower and then deployed Security Hub and expected that AWS Config would be enabled in the Management account, but find that it isn’t?
It’s a relatively simple fix that involves adding your account id to several StackSets and configuring a missing role:
StackSets:
- AWSControlTowerBP-BASELINE-SERVICE-ROLES
- AWSControlTowerBP-BASELINE-ROLES
- AWSControlTowerBP-BASELINE-CONFIG
Roles:
- AWSControlTowerExecution
I’m generally deploying to the Sydney (ap-southeast-2) region, so my procedure will use this region. If you are deploying Security Hub and Control Tower in other regions substitute as appropriate.
Roles
Let’s start by setting up the missing role.
Navigate to IAM, roles. https://console.aws.amazon.com/iam/home?region=ap-southeast-2#/roles
Create a new role call AWSControlTowerExecution.
Set the Trust Relationship as follows:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::123456789012:root"
},
"Action": "sts:AssumeRole",
"Condition": {}
}
]
}
Attach the AdministratorAccess AWS managed policy.
StackSets
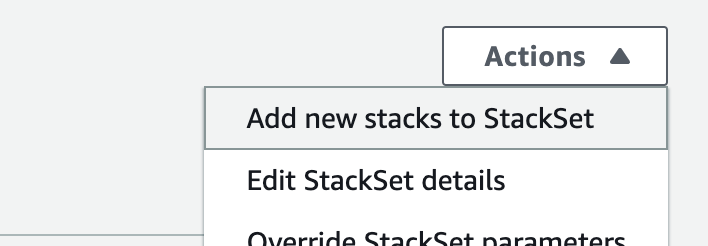
Navigate to the StackSets console and locate the AWSControlTowerBP-BASELINE-SERVICE-ROLES StackSet:
Now add a new stack StackSet:
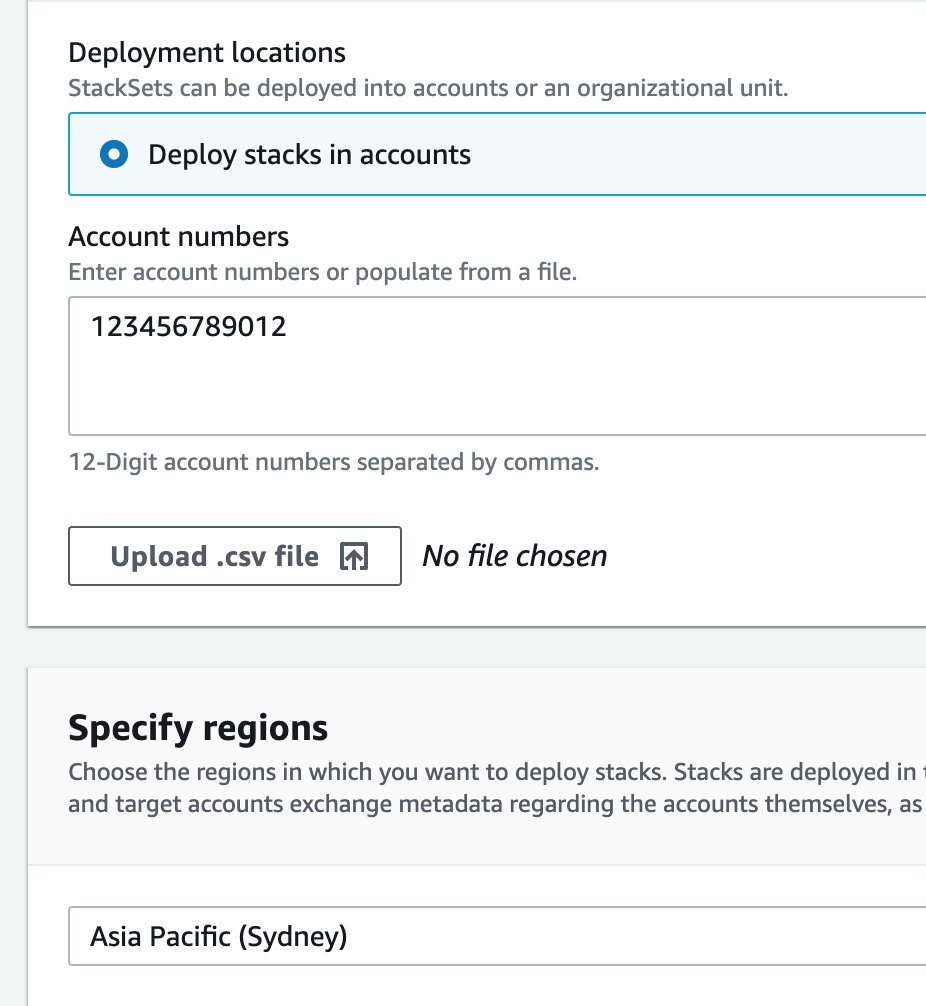
Then add your account and the region:
And do the same for the AWSControlTowerBP-BASELINE-ROLES StackSet:
Once you’ve completed that you need to then deploy the last StackSet, but you need to deploy this one to all the regions you are managing. As my ControlTower deployment is a little older, I only have to deploy to these regions:
- ap-southeast-2
- eu-west-1
- us-west-1
- us-west-2
- us-east-1
- us-east-2
Yours may be different, so check which regions by looking at the StackSet instances.
Now enjoy your AWS Config in your management account.