I often read or hear about people starting their AWS journey by setting up new AWS account and getting themselves into trouble when someone breaks in and runs up a huge bills.
With that in mind I thought I would write a CloudFormation template with the services I recommend in a base setup and also describe some of the things I setup.
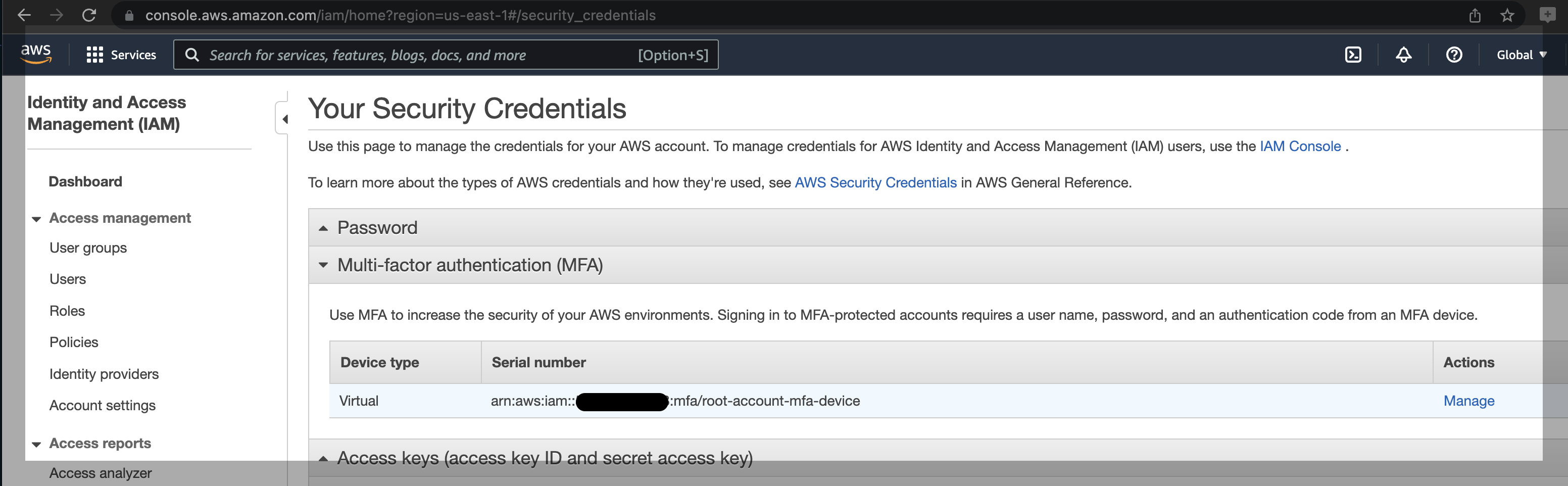
Root MFA
Once you’ve signed up with your “Root” user, setup MFA:
https://console.aws.amazon.com/iam/home?region=us-east-1#/security_credentials
IAM User
Now go and setup an IAM user:
https://docs.aws.amazon.com/IAM/latest/UserGuide/id_users_create.html
https://console.aws.amazon.com/iamv2/home?#/users
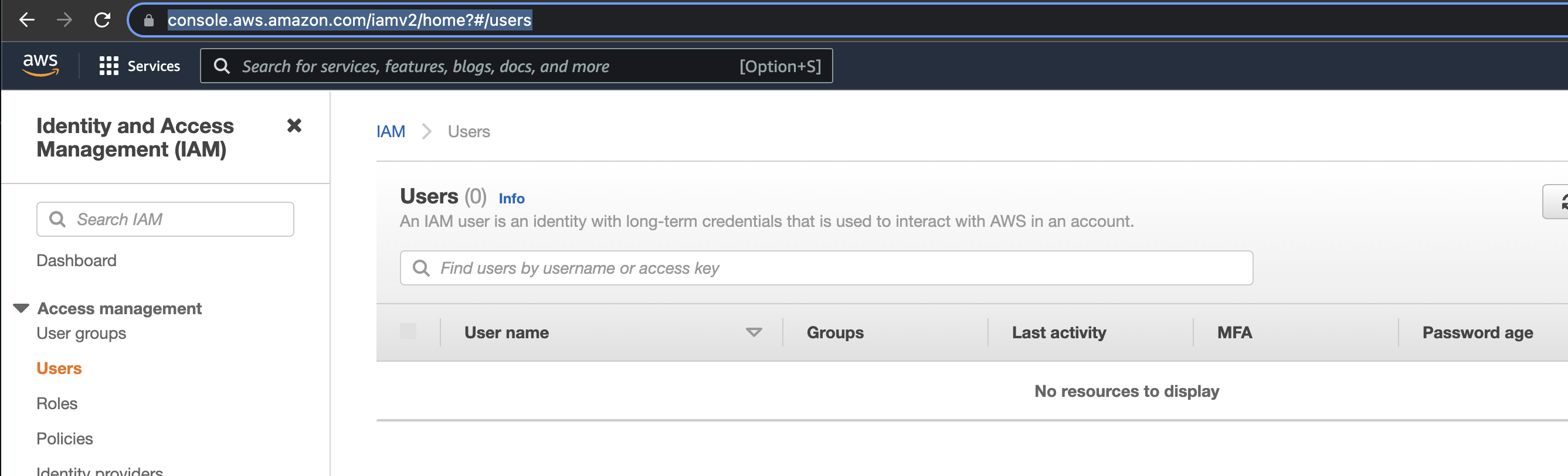
And of course make sure you setup MFA again on the IAM user.
https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_mfa_enable.html
From now on, make sure you use your IAM users with MFA. There are more complex setups (using roles and policies enforcing MFA, but I’ll leave that as an exercise for the reader as it’s an advanced topic).
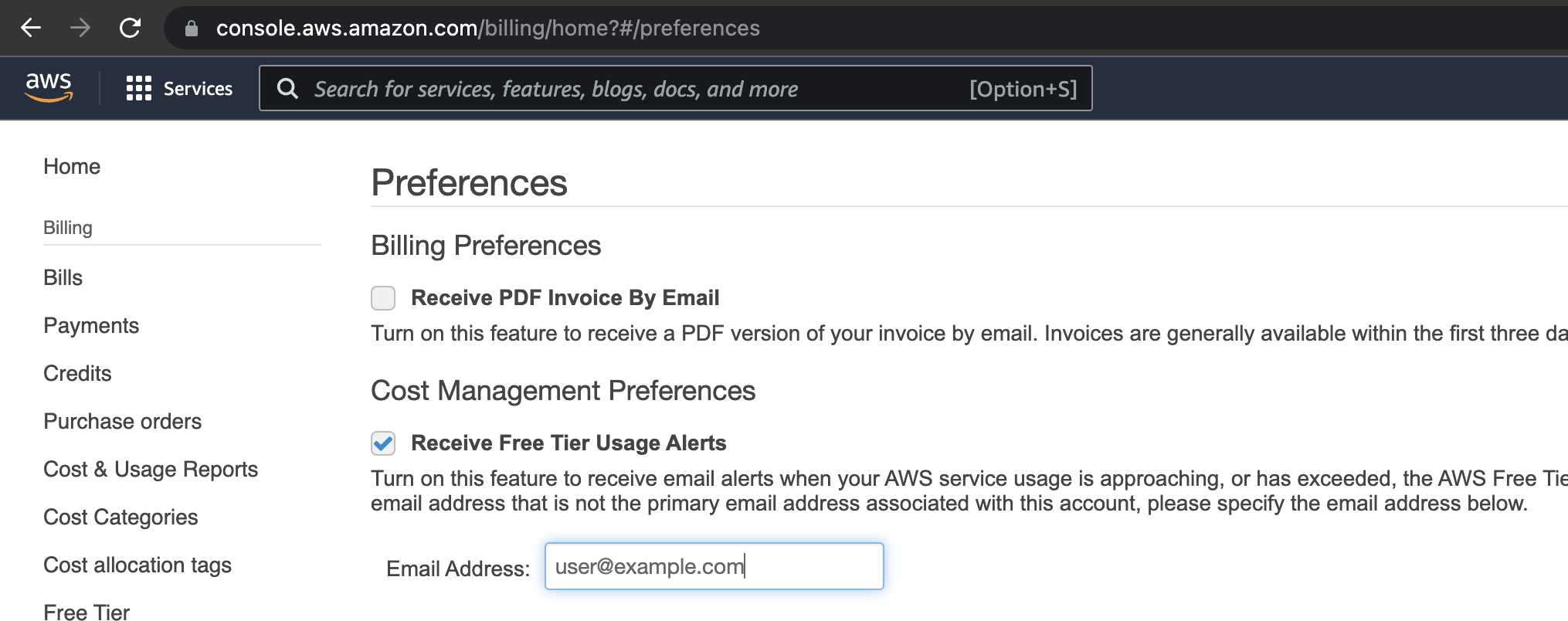
Free Tier Alerts
Last thing that you can’t easily do with CloudFormation, is to setup Free Tier alerts:
https://docs.aws.amazon.com/awsaccountbilling/latest/aboutv2/tracking-free-tier-usage.html
https://console.aws.amazon.com/billing/home?#/preferences
All the good stuff
Finally deploy this CloudFormation template which will setup the following services:
- CloudTrail (All Regions)
- CloudTrail Bucket (With 90 Day deletion lifecycle policy)
- Budgets
- Cost Anomaly Detection
- Billing Alert
- Root Activity Alert
Make sure you deploy this in us-east-1!
Note, this is a really simple setup to get you going and provide some level of protection. It may not work for every scenario and I recommend, you spend some time understanding what it is doing and modifying it as you see fit.
Hopefully this saves some people from having their AWS accounts compromised and provides a safer environment for everyone getting started in AWS.
